6 Ecommerce Security Rules to Double Down on Hosted Platform Site Protection
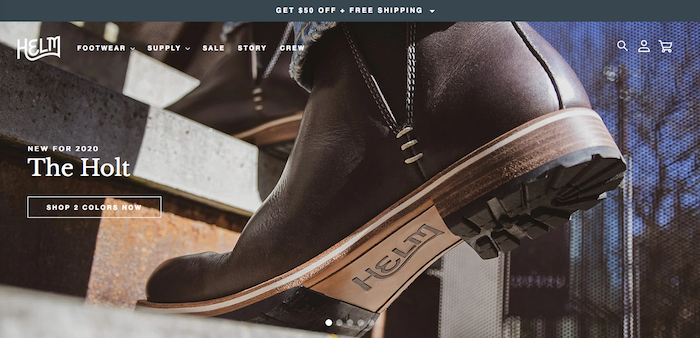
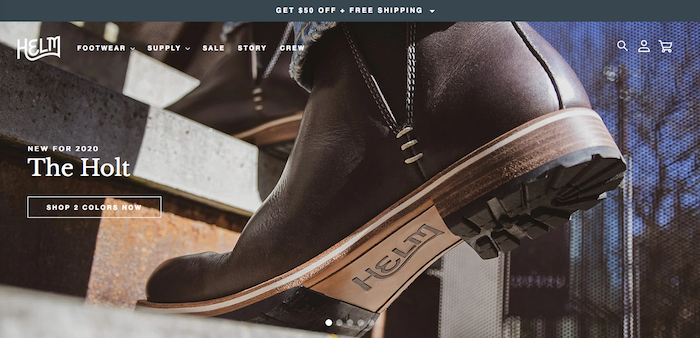
Helm Boots sells footwear and more on Shopify
For ecommerce retailers, one of the great benefits of having your site on a hosted platform is that the platform, by and large, takes care of site security. On Shopify, for example, websites are Level 1 PCI compliant right out of the box. This means that your financial transactions and data remain secure, as Shopify takes responsibility for security.
Nonetheless, at Command C, we believe that there is no such thing as too much security for an online store. First and foremost, strong site security creates customer trust. In fact, last year 17% of online shoppers said they will abandon the cart when they sense a “lack of trust with my credit card information.”
Secondly, any kind of security breach can be destructive to a retail business. Our goal is always to do everything possible to prevent such a breach from happening. Indeed, hosted platforms do their part. Yet, as a retailer, there are additional measures you can take to fortify your business. These measures enhance the already-robust security found within hosted platforms. Given that the fallout from a breach would be dire, it’s important to do every last possible thing to protect your ecommerce business.
We can divide these additional security practices into three main categories. The first category is to limit and restrict access to your site administration. The second category involves preparing your company to be able to recover from a security breach in case one happens.
The third category, the customer-facing side of security, deals with communicating security to your customers. The price for entry in this category is an up-to-date SSL certificate for your site. Especially as online shoppers get more savvy, they want to see the locked padlock in a site URL before they share their credit card information. Yet, not only can merchants ease customers’ concern with the SSL certificate, you can go further to communicate the security of your site.
As a retailer, you can double down on security for already-secure platforms. Here we’ve outlined how to do so with our top six rules for ecommerce security on hosted platforms. Do you have all six of these measures in place for your online store?
Ecommerce Backend Site Security: Limit Access to Your Store Admin
Rule #1: Do not share internal passwords
Password issues begin innocently enough. In the early days of your business, you may only have one or two employees who need access to the platform. It just seems easiest to let people share the same login. Then, as your company grows, more people access the site with shared credentials. This leads to problems, so our first rule is: Do not share internal passwords.
Why wouldn’t your team want to share passwords? Imagine this scenario: The seven people who work in your ecommerce operations all log-in with the same information. Then one employee leaves the company, forcing you to change the password and communicate that change to everyone. If everyone logs-in using their own account, you can just disable the account of the former employee.
Alternatively, suppose something goes wrong within your store data. Perhaps product pricing gets mislabeled – or worse. Maybe there is a security breach as a result of a change that was made to your site. If everyone has the same login info, you won’t know who actually made the mistake. When people have different logins, you can quickly determine who is behind the action.
This rule isn’t about being punitive. It’s about acknowledging that anyone can make a mistake. When that happens, you want to be able to determine the source of any issues as quickly as you can. When everyone keeps separate logins and passwords, you have greater clarity and accountability among team members.
Lastly, remember to use secure passwords. A password generator can help here. It’s also a good idea to enable two-factor authentication for all your accounts. This helps secure the accounts from unauthorized access in case a password is stolen.
Rule #2: Tailor security permissions to each internal role
Much like sharing passwords, a lot of merchants develop this issue by default. At first, while your company is small, everyone may be able to access all areas of your online store. It’s critical, however, to tailor your site security permissions regardless of company size. This means that you will define what each employee can do within your store. For example, you can adjust the settings so one user has access to orders and inventory, a second person has access to only your orders, and a third has access to everything.
There are a couple of reasons behind this rule. First, when people have limited access, they can’t do more than their role in the company allows. It protects your store from having someone without the right expertise potentially making a mistake on the backend.
Secondly, if an employee’s account gets compromised, then whoever gets access to that account can only cause so much damage. The security breach will be contained within the permissions that have been granted.
This rule holds true for both your employees and any third-party apps that communicate with your store. Give them access to only what they need.
Rule #3: Review third-party app access regularly
Nearly every retailer uses apps to create their ecommerce ecosystem. They can perform essential functions, but are you still using all the apps that have access to your site?
Third-party apps connect to your site to access various site data. Again, this can be super useful, but if you’re no longer actively using a particular app, it could be a potential security weakness. Work with your team to set up a regular app review process to make sure you stay current on your store apps. We suggest doing this at least twice a year, if not every quarter.
If you’re no longer using an app, delete it. This is even more critical for private apps, in other words, apps that are not officially vetted by the hosted platform, i.e. Shopify or BigCommerce.
Perhaps a former developer created a private app that lets them upload and download theme files to your site. A lot of developers do this, and there’s nothing wrong with it while they are actively working for you. But, if they are not a part of your team any longer, their app should be deleted.
Protecting your site against security breaches
Rule #4: Do not rely on your ecommerce platform as the sole source of product and customer data
We recommend creating a separate storage system for your store data, including theme files, orders, products, customers – you name it. You want a copy of all of the data and files that are in your store admin. This way, if your data is lost or corrupted, or you suffer a security breach of any kind, you can easily recover the information. You’ll be able to get back up and running quickly by repopulating your store with the duplicate files. For merchants on Shopify, there’s a Shopify app called Rewind Backups that will create this kind of system for you.
Make sure to have an alternative in place, even if it’s just Excel documents for product data. Whatever system you choose, you should update it every time you update your product catalog. In fact, it’s not just about having a “backup.” The security goal here is to have your store data stored elsewhere, so that if something happens to your store, or you decide to change platforms, you have another copy. Then use that system to update your store. Let the second system, if you will, be your system of record.
Keep in mind, too, that you may have different parts of your store data in different locations. With customer data, for instance, if you have a CRM (customer relationship management) and/or an email marketing platform, this information will live in that application, respectively. Often times, the site order data will populate to these apps to support campaigns like win-back emails or abandon-cart promotions.
The important thing to remember is do not use your ecommerce system as the only system of record for your store. Have another system – or systems – in place to maintain your site data.
Frontend Security Practices
Rule #5: Log out customers after a set amount of time
This one is quick and simple: Make sure your customer account logins expire after a certain amount of time. We suggest doing this at least once a week. As a result, you’ll better protect your customers’ information. Then when customers log back in after a set amount of time, the site will force them to verify that they are who they say they are. Yes, this may be teeny bit inconvenient, but the extra layer of security is worth it.
(Please note: We’re not talking about making customers change their password – that’s an obstacle to conversion.)
Rule #6: Work with your attorney to pre-define your response to any security issues
If your site suffered any kind of data breach today, how would your company respond? It’s vital that you are prepared for this kind of unexpected event. This includes having plans and policies in place for how you would handle and respond to a breach. How would you notify your customers? How would you recover information? (For starters, see Rule #4)
Security breaches don’t have to involve credit card information; exposing customer names and emails alone would create a problem. Working with your attorney, define your strategy and make sure your employees know the response plan. It’s always been a good idea to be ready, but in some cases, after the implementation of GDPR in 2018, this kind of plan is now legally mandated. Make it part of your privacy policy or your Terms of Service. It’s key to be proactive rather than reactive.
As you see, these six rules of ecommerce security don’t involve changing the platform itself. These rules enhance the already-powerful security provided by hosted platforms. Platform like Shopify and BigCommerce are a rock solid foundation. Now, with these six rules in place, you’ll work in tandem with your platform to further secure your online retail business.
